MICROSOFT NEWS: 70-663 Exam Questions has been Updated Today! Get Latest 70-663 VCE and 70-663 PDF Instantly! Welcome to Download the Newest Braindump2go 70-663 VCE&70-663 PDF Dumps: http://www.braindump2go.com/70-663.html (291 Q&As)
2016 Latest released Microsoft Official 70-663 Practice Exam Question Free Download From Braindump2go Now! All New Updated 291 Questions And Answers are Real Questions from Microsoft Exam Center!
Exam Code: 70-663
Exam Name: Pro: Designing and Deploying Messaging Solutions with Microsoft Exchange Server 2010
Certification Provider: Microsoft
Corresponding Certifications: MCITP, MCITP: Enterprise Messaging Administrator on Exchange 2010
70-663 Dumps,70-663 Dumps PDF,70-663 Dumps VCE,70-663 PDF,70-663 VCE,70-663 Study Guide,70-663 Braindump,70-663 Book,70-663 Exam Questions,70-663 Practice Test,70-663 Practice Exam,70-663 eBook,70-663 Preparation
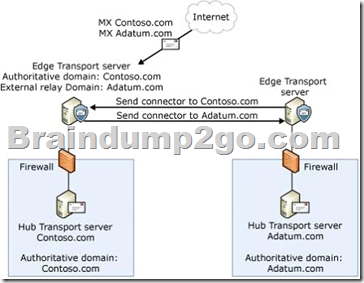
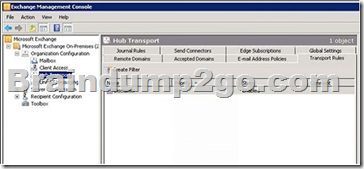
QUESTION 101
Your Exchange Server 2010 organization contains two Hub Transport servers in a single site.
The organization receives all e-mail sent to a SMTP domain named contoso.com.
Your company purchases another company that uses a SMTP domain named fabrikam.com.
You plan to manage message hygiene for both SMTP domains.
You need to recommend changes to the organization to support the planned deployment.
The solution must prevent e-mail sent to fabrikam.com from being delivered to your internal organization.
What should you recommend?
A. Deploy a new Hub Transport server, and then create remote domains.
B. Deploy a new Hub Transport server, and then configure transport rules.
C. Deploy an Edge Transport server, and then create accepted domains.
D. Deploy an Edge Transport server, and then configure a federation trust.
Answer: C
Explanation:
while a hub transport can provide message hygiene for this question deploying Edge Transport Servers is the proper solution
QUESTION 102
You have an Exchange Server 2010 organization.
You have a group named Help Desk that contains all the help desk users in the organization.
You need to ensure that the Help Desk group can manage all the mailboxes and mail-enabled contacts in the organization.
The solution must minimize the number of permissions assigned to the Help Desk group.
Which management role should you assign to the Help Desk group?
A. Mail Recipients
B. Mail Recipient Creation
C. Organization Client Access
D. Recipient Policies
Answer: A
Explanation:
Section: Designing and Deploying Messaging Compliance, System Monitoring, and Reporting
The Mail Recipients management role enables administrators to manage existing mailboxes, mail users, and mail contacts in an organization. This role can’t create these recipients. Use the Mail Recipient Creation role to create them.
This role type doesn’t enable you to manage mail-enabled public folders or distribution groups. Use the following roles to manage these objects:
– Mail Enabled Public Folders Role
– Distribution Groups Role
http://technet.microsoft.com/en-us/library/dd876911.aspx
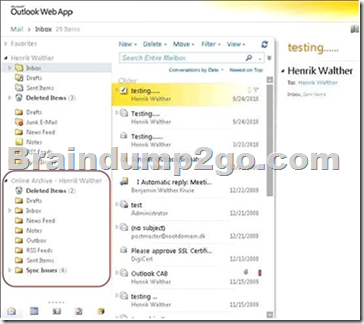
QUESTION 103
You have an Exchange Server 2010 organization.
You need to recommend a storage solution that meets the following requirements:
– Provides users with an alternate location for storing e-mail messages
– Provides users with access to the alternate location by using Outlook Web App (OWA)
What should you recommend?
A. journal rules
B. managed folders
C. personal archives
D. personal folders (.pst)
Answer: C
Explanation:
In Microsoft Exchange Server 2010, personal archives provide users an alternative storage location in which to store historical messaging data. A personal archive is an additional mailbox (called an archive mailbox) enabled for a mailbox user.

QUESTION 104
You have an Exchange Server 2010 organization.
Your company’s legal department sends compliance e-mail messages by adding recipients to the blind carbon copy (Bcc) field.
The company’s compliance policy includes the following requirements:
– All e-mail messages sent to external recipients must be archived in a central repository
– Compliance officers must be able to identify all the recipients of archived e-mail messages
You need recommend a solution to meet the compliance policy requirements. What should you recommend?
A. journal rules
B. message tracking
C. Personal Archives
D. transport rules
Answer: A
Explanation:
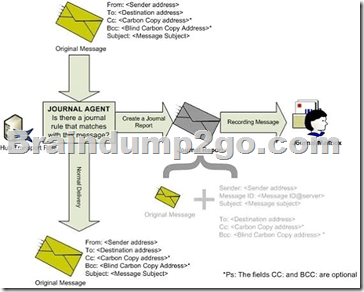
A journal report is the message generated by the Journaling agent on a Hub Transport server and delivered to the journaling mailbox. The original message is included unaltered as an attachment to the journal report. This type of journal report is called an envelope journal report.
When using standard journaling, journal reports are generated for all messages sent or received by mailboxes on a mailbox database enabled for journaling. When using premium journaling, journal reports are generated for messages that match a journal rule.
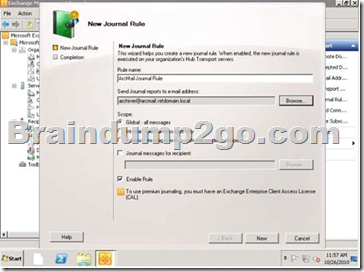
When the Journaling agent journals a message, it tries to capture as much detail as possible about the original message. This information is very important in determining the intent of the message, its recipients, and its senders. For example, whether the recipients that are identified in the message are directly addressed in the To field, the Cc field or are included as part of a distribution list may determine the nature and extent of their involvement in the e-mail communication.
QUESTION 105
You have an Exchange Server 2010 organization for a company named Contoso, Ltd.
Contoso has the following security policy:
– Messages that contain the word budget cannot be sent to external recipients
– Messages that contain the name Northwind Traders must be sent to the legal department automatically
You need to recommend a solution to meet the security policy.
What should you recommend?
A. Create two transport rules.
B. Create two message classifications.
C. Create one transport rule and configure a legal hold.
D. Create one message classification and configure a legal hold.
Answer: A
Explanation:
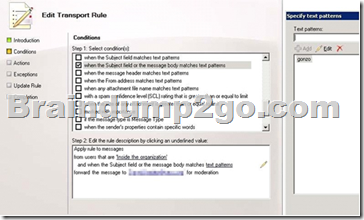
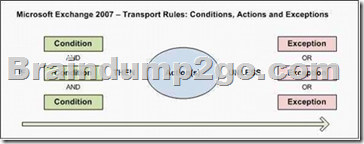
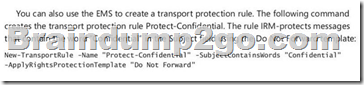
Transport rule conditions and exceptions consist of one or more predicates. Predicates instruct the Transport Rules agent on a Hub Transport server (or the Edge Rules agent on an Edge Transport server) to examine a specific part of an e-mail message, such as sender, recipients, subject, other message headers, and message body, to determine whether the rule should be applied to that message.
New-TransportRule -Name “Social Security Number Block Rule” – SubjectOrBodyMatchesPatterns ‘\d\d
\d-\d\d-\d\d\d\d’ -RejectMessageEnhancedStatusCode “5.7.1” -RejectMessageReasonText “
This message has been rejected because of content restrictions”
In the initial installation of Exchange 2010, all message classifications are informational only. They aren’t associated with any transport rules and only provide additional information about a message to the message recipients. By default, in Exchange 2010, the Microsoft Exchange Transport service doesn’t take any special action on the message. However, you can create transport rules based on message classifications. For example, you can configure a transport rule that checks all incoming messages for a specific message classification and direct that these messages be delivered to a designated recipient. For more information, see Create a Transport Rule.
Message classifications can be logically separated into two classes based on how they are attached to a specific message:
1- A message classification can be manually added by the sender of a message before the message is sent.
2- A message classification can be added as the result of a rule. For example, when the Attachment Filter agent removes an attachment from a message, the Attachment Removed message classification is attached to the message. When the sender receives the message, Outlook 2007 displays an explanation of why the attachment was removed in the recipient description in the InfoBar. As the Exchange administrator, you can customize the recipient description.
QUESTION 106
You have an Exchange Server 2010 organization.
You need to plan a message hygiene solution that meets the following requirements:
– Spoofing must be minimized
– Open SMTP relays must be added to IP block lists automatically
What should you include in the plan?
A. Sender ID filtering and recipient filtering
B. Sender ID filtering and sender reputation
C. sender filtering and recipient filtering
D. sender reputation and recipient filtering
Answer: B
Explanation:
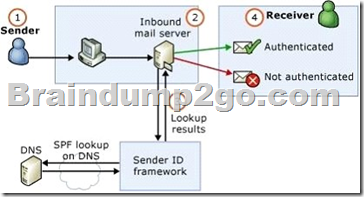
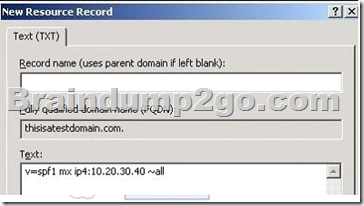
Sender ID is intended to combat the impersonation of a sender and a domain, a practice that’s frequently called spoofing. A spoofed mail is an e-mail message that has a sending address that was modified to appear as if it originates from a sender other than the actual sender of the message.
Spoofed mails typically contain a From: address that purports to be from a certain organization. In the past, it was relatively easy to spoof the From: address, in both the SMTP session, such as the MAIL FROM: header, and in the RFC 822 message data, such as From: “Masato Kawai” [email protected], because the headers weren’t validated.
Sender reputation evaluates several sender characteristics to calculate an SRL. Among the characteristics that sender reputation evaluates are the results of a test for open proxy servers. Frequently, spammers route messages through open proxy servers on the Internet. By routing spam through open proxy servers, spammers can send messages that appear to originate from a different server than their own.
When sender reputation calculates an SRL, sender reputation tries to connect to the sender’s originating IP address by using a variety of common proxy protocols, such as SOCKS4, SOCKS5, HTTP, Telnet, Cisco, and Wingate. Sender reputation formats a protocol-specific request in an attempt to connect back to the Edge Transport server from the open proxy server by using an SMTP request. If an SMTP request is received from the proxy server, sender reputation verifies that the proxy server is an open proxy server and adjusts the SRL rating according to this result. By default, detection of open proxy servers is enabled on sender reputation.
http://technet.microsoft.com/en-us/library/bb124512.aspx
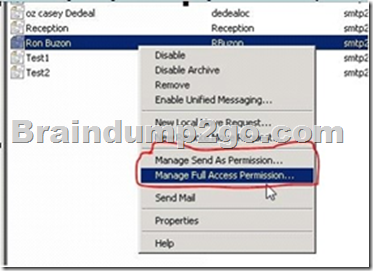
QUESTION 107
Your network contains an Exchange Server 2010 server.
You need to plan a mailbox sharing solution for the organization to meets the following requirements:
– Ensure that assistants can read and modify the e-mail messages of their managers
– Ensure that assistants can impersonate their managers when they send e-mail messages
What should you include in the plan?
A. Full Access and Send As permissions
B. Full Access and send on behalf of permissions
C. Role Based Access Control (RBAC) assignments and Send As permissions
D. Role Based Access Control (RBAC) assignments and send on behalf of permissions
Answer: A
Explanation:
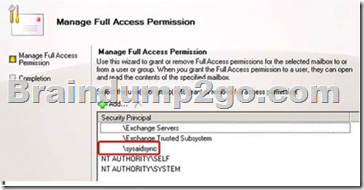
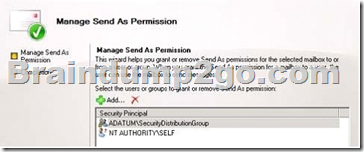
You have to:
1. Grant access to a mailbox and its content.
2. Grant the right to send messages as the mailbox owner.
In the Exchange Management Console, right-click the mailbox you want to work with and then select “Manage
Full Access Permission” or “Manage Send As Permission”.
QUESTION 108
Your company has an Active Directory forest named contoso.com.
You plan to deploy an Exchange Server 2010 organization that will contain two servers.
Each server will have the Client Access server role, the Hub Transport server role, and the Mailbox server role installed.
You plan to add both servers to a database availability group (DAG).
You need to recommend a high-availability solution for the Client Access server role.
Your solution must ensure that users are not prompted to authenticate if a Client Access server becomes unavailable.
What should you recommend?
A. Create and configure a Client Access server array, and then install a hardware load balancer.
B. Create and configure a Client Access server array, and then install Windows Network Load
Balancing on both servers.
C. Deploy Microsoft Internet Security and Acceleration (ISA) Server 2006, and then implement
DNS round robin.
D. Deploy Microsoft Internet Security and Acceleration (ISA) Server 2006, and then install
Windows Network Load Balancing.
Answer: A
Explanation:
While it is possible to install the Windows Network Load Balancing for a client access array that solution will not work for this question.
Windows Network Load Balancing
Windows Network Load Balancing (WNLB) is the most common software load balancer used for Exchange servers. There are several limitations associated with deploying WNLB with Microsoft Exchange.
WNLB can’t be used on Exchange servers where mailbox DAGs are also being used because WNLB is incompatible with Windows failover clustering. If you’re using an Exchange 2010 DAG and you want to use WNLB, you need to have the Client Access server role and the Mailbox server role running on separate servers. Due to performance issues, we don’t recommend putting more than eight Client Access servers in an array that’s load balanced by WNLB.
WNLB doesn’t detect service outages. WNLB only detects server outages by IP address.
This means if a particular Web service, such as Outlook Web App, fails, but the server is still functioning, WNLB won’t detect the failure and will still route requests to that Client Access server. Manual intervention is required to remove the Client Access server experiencing the outage from the load balancing pool.
WNLB configuration can result in port flooding, which can overwhelm networks. Because WNLB only performs client affinity using the source IP address, it’s not an effective solution when the source IP pool is small. This can occur when the source IP pool is from a remote network subnet or when your organization is using network address translation.
http://technet.microsoft.com/en-us/library/ff625247.aspx
QUESTION 109
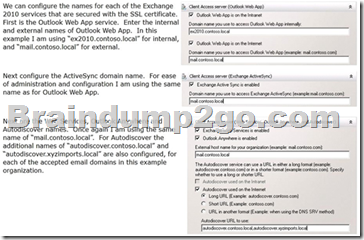
You have an Exchange Server 2010 organization named contoso.com.
The organization contains two Client Access servers named CAS1 and CAS2 that are in a Clien Access server array.
All internal and external users connect to their mailboxes by using mail.contoso.com.
You need to install a certificate on the Client Access servers to meet the following requirements:
– Support 500 client computers that are not joined to the Active Directory domain
– Support clients that use Microsoft Office Outlook in Cached Exchange Mode, Autodiscover, and
Exchange ActiveSync
– Minimize client and user support costs
What should you do?
A. From a trusted third-party certification authority (CA), generate a certificate request that
contains the mail.contoso.com and Autodiscover names.
B. From a trusted third-party certification authority (CA), generate a certificate request that
contains the CAS1.contoso.com and CAS2.contoso.com names.
C. From an internal Active Directory-integrated certification authority (CA), generate a certificate
request that contains the mail.contoso.com and Autodiscover names.
D. From an internal Active Directory-integrated certification authority (CA), generate a certificate
request that contains the CAS1.contoso.com and CAS2.contoso.com names.
Answer: A
Explanation:
It is recommended to use a SAN (Subject Alternative Name) certificates.
QUESTION 110
You have an Exchange Server 2010 organization.
Your company has a relationship with another company.
The partner company has an Exchange Server 2010 organization.
You need to recommend a security solution to meet the following requirements:
– Ensure that all e-mail delivery between your servers and the partner company’s servers is encrypted
– Ensure that all communication between your servers and the partner company’s servers is authenticated
What should you include in the solution?
A. Active Directory Rights Management Services (AD RMS)
B. Domain Security
C. Forms-based Authentication
D. Secure/Multipurpose Internet Mail Extensions (S/MIME)
Answer: B
Explanation:
Domain Security refers to the set of functionality in Microsoft Exchange Server 2010 and Microsoft Office Outlook 2007 that provides a relatively low-cost alternative to S/MIME or other message-level security solutions. The purpose of the Domain Security feature set is to provide administrators a way to manage secured message paths over the Internet with business partners. After these secured message paths are configured, messages that have successfully traveled over the secured path from an authenticated sender are displayed to users as Domain Secured in the Outlook and Microsoft Office Outlook Web App interface. Domain Security uses mutual Transport Layer Security (TLS) authentication to provide session-based authentication and encryption. Mutual TLS authentication differs from TLS as it’s usually implemented. Typically, when TLS is implemented, the client verifies that the connection securely connects to the intended server by validating the server’s certificate. This is received as part of TLS negotiation. In this scenario, the client authenticates the server before the client transmits data. However, the server doesn’t authenticate the session with the client. With mutual TLS authentication, each server verifies the connection with the other server by validating a certificate that’s provided by that other server. In this scenario, where messages are received from external domains over verified connections in an Exchange 2010 environment, Outlook 2007 displays a Domain Secured icon.
http://technet.microsoft.com/en-us/library/bb124392.aspx
Want to be 70-663 certified? Using Braindump2go New Released 70-663 Exam Dumps Now! We Promise you a 100% Success Passing Exam 70-663 Or We will return your money back instantly!
FREE DOWNLOAD: NEW UPDATED 70-663 PDF Dumps &70-663 VCE Dumps from Braindump2go: http://www.braindump2go.com/70-663.html (291 Q&As)