December/2021 Latest Braindump2go 350-901 Exam Dumps with PDF and VCE Free Updated Today! Following are some new 350-901 Real Exam Questions!
QUESTION 211
An enterprise refactors its monolithic application into a modem cloud-native application that is based on microservices.
A key requirement of the application design is to ensure that the IT team is aware of performance issues or bottlenecks in the new application.
Which two approaches must be part of the design considerations” (Choose two.)
A. Periodically scale up the resources of the host machines when the application starts to experience high loads
B. Instrument the application code to gather telemetry data from logs, metrics or tracing
C. Adopt a service-oriented architecture to handle communication between the services that make up the application
D. Deploy infrastructure monitoring agents into the operating system of the host machines
E. Implement infrastructure monitoring to ensure that pipeline components interoperate smoothly and reliably
Answer: BE
QUESTION 212
Refer to the exhibit. An application is created to serve an enterprise. Based on use and department requirements, changes are requested quarterly. Which application design change improves code maintainability?
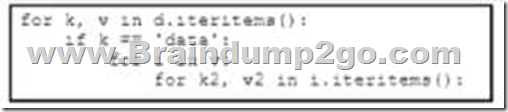
A. Use global variables
B. Use double quotes instead of single quotes to enclose variables
C. Use different indent levels for variables
D. Use more verbose names for variables
Answer: D
QUESTION 213
An architect must optimize traffic that targets a popular API endpoint. Currently, the application downloads a large file hourly, but often the file is unchanged and the download causes unnecessary load and delays. Which cURL command must be used to determine the last modified date of the file and to optimize the API usage?
A. curl GET request
B. curl HEAD request
C. curl –silent request
D. curl -H ‘Cache-Control: no-cache’ request
Answer: B
QUESTION 214
Refer to the exhibit. A developer created a Python script to retrieve information about Meraki devices in a local network deployment. After requesting a security review of the code the security analyst has observed poor secret storage practices.
What is the appropriate secret storage approach?
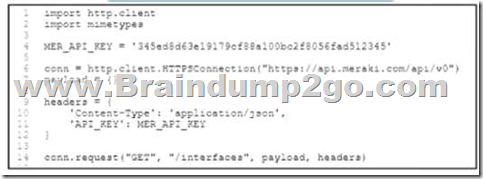
A. Set the Base64 encoded version of the API key as MER_API_KEY m the code and Base64 decode before using m the header
B. Leverage an external secret vault to retrieve MER_API_KEY and embed the vault key as a new variable before running the code
C. Leverage an external secret vault to retrieve MER_APl_KEY and set the vault key as an OS environment variable before running the code
D. Set an OS environment variable for MER_API_KEY to the API key before running the code and no longer set MER_API_KEY within the code
Answer: C
QUESTION 215
When an application is designed that requires high availability, what is a reason to use a cross-region cloud?
A. Provide disaster recovery protection
B. Protect from a single component failure
C. Minimize costs
D. Account for failure in another zone
Answer: A
QUESTION 216
Refer to the exhibit. A Docker swarm cluster is configured to load balance services across data centers in three different geographical regions west central and east. The cluster has three manager nodes and three worker nodes. A new service named cisco.devnet is being deployed.
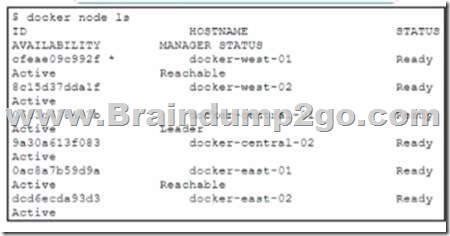
The service has these design requirements:
– All containers must be hosted only on nodes in the central region
– The service must run only on nodes that are ineligible for the manager role
Which approach fulfills the requirements?
A. Create a second swarm cluster that is hosted only in the central region.
B. Create the service manually in the central region and set replicas to 0.
C. Use placement constraints to control nodes to which the service can be assigned.
D. Enable the control flag in the containers of the west and east regions to prevent the service from starting
Answer: D
QUESTION 217
Refer to the exhibit. Refer to the exhibit A Docker swarm service is currently running m a local data center. The service is hosting an HTML website it the container fads then the service becomes unavailable. The design must meet these requirements:
– The service must be highly available and resilient against a data center outage.
– The service must be accessible from a single URL
– The HTTP session must remain on the server from which the original request was sent
– Failure of the server must force the client to reconnect
Which two design approaches must be used to meet the requirements? (Choose two.)
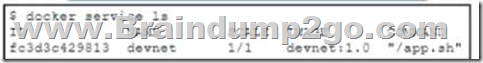
A. Create another swarm cluster within a data center and deploy a secondary instance of the service.
B. Create another node in the swarm duster to scale the service across the nodes over two replicas.
C. Configure an external load balancer to route requests to the swarm service by using session persistence
D. Scale the Docker swarm service to 2 and set endpoint-mode to DNSRR instead of the default value of VIP
E. Configure a routing mesh to route requests to the swarm service by using NAT on the network side
Answer: BC
QUESTION 218
A developer must deploy a containerized application foe network device inventory management. The developer sets up a Kubernetes duster on two separate hypervisors. The SLA is not currently meeting a specified maximum value for network latencyjitter CPU/memory and disk I/O are functioning property. Which two design approaches resolve the issue” (Choose two.)
A. Colocate services in the same pod
B. Replace the HDD drives with SSD drives
C. Enable IPv6 within the duster
D. Deploy the duster to a bare metal server
E. Upgrade the server NIC card
Answer: AE
QUESTION 220
A developer deploys a web application in a local data center that is now experiencing high traffic load from users accessing data through REST API calls.
Which approach enhances the responsiveness and performance of the API?
A. Use HTTP POST or other non-read methods for read requests when possible
B. Ensure that all read requests are clearly identified by the PUT method
C. Configure API payload to return errors in HTTP 200 responses
D. Use HTTP standard authorization header to submit authentication credentials
Answer: D
QUESTION 221
A custom dashboard of the network health must be created by using Cisco DNA Center APIs. An existing dashboard is a RESTful API that receives data from Cisco DNA Center as a new metric every time the network health information is sent from the script to the dashboard.
Which set of requests creates the custom dashboard?
A. PUT request to Cisco DNA Center to obtain the network health information and then a POST
request to the dashboard to publish the new metric
B. POST request to Cisco DNA Center to obtain the network health information and then a GET request to the dashboard to publish the new metric
C. GET request to Cisco DNA Center to obtain the network health information and then a PUT request to the dashboard to publish the new metric
D. GET request to Cisco DNA Center to obtain the network health information and then a POST request to the dashboard to publish the new metric
Answer: D
QUESTION 222
A developer wants to automate virtual infrastructure to provision and manage it.
The system will be implemented in large-scale deployment while offering redundancy and scalability with ease of management.
The solution must meet these requirements:
– Support the provisioning of up to 500 new virtual machines into private datacenters or the public cloud
– Support the modeling of a complex environment that consists of multiple virtual machines while supporting disaster recovery
– Maintain steady-state environments
Which configuration management solution must the developer use?
A. Puppet
B. Terraform
C. Docker
D. Arable
Answer: B
QUESTION 224
What are two building blocks of the 12-factor app? (Choose two.)
A. Stateful Processes
B. Easy access to underlying systems
C. Dev and Prod must be different
D. One codebase
E. Isolated Dependencies
Answer: DE
QUESTION 227
Which command is used 10 enable application hosting on a Cisco IOS XE device?
A. iox
B. iox-service
C. application -honing
D. app- hosting
Answer: A
QUESTION 228
A developer releases a new application for network automation of Cisco devices deployed m a local data center. The application utilizes complex design patterns such as microservices that host multiple third-party libraries and programming languages. The development must be simplified by implementing an observability-driven development lifecycle.
Which two considerations must be taken to meet the requirements? (Choose two.)
A. description of low-level errors
B. which KPls to monitor
C. relevant metrics to expose
D. which monitoring tools to use
E. identifying customer priorities
Answer: BC
QUESTION 229
A developer must recommend an appropriate tool to deploy a configuration to hundreds of servers. The configuration management solution must meet these requirements:
– The servers must initiate the connection to obtain updates
– The configuration must be defined in a declarative style
Which tool should be used?
A. Chef
B. Terraform
C. Puppet
D. Ansible
Answer: A
QUESTION 230
Refer to the exhibit. An engineer writes a script to retrieve data from a REST API and must build support for cases where the response that contains data from the server may take a longer time than normal.
Which code must be added to the snippet where the code is missing to catch such a timeout?

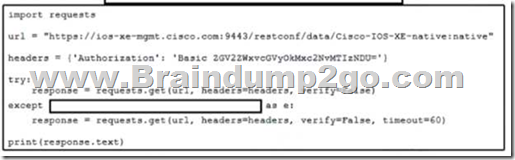
A. request.exeception.ConnectTimeout
B. request.executions.DataTimeout
C. request.exeception.HTTPError
D. request.exception.ReadTimeout
Answer: A
QUESTION 231
Refer to the exhibit. The application follows a containerized microservices architecture that has one container per microservice. The microservices communicate with each other by using REST APIs. The double- headed arrows m the diagram display chains of synchronous HTTP calls needed for a single use/request. Which action ensures the resilience of the application in the scope of a single user request?
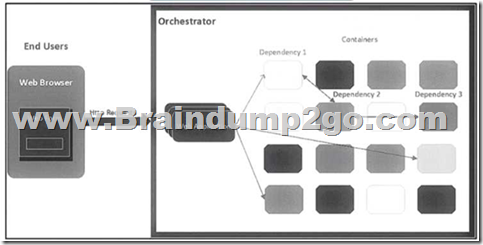
A. Redesign the application to be separated into these three layers Presentation. API. and Data
B. Implement retries with exponential backoff during HTTP API calls
C. Set up multiple instances of each microservice m active/active mode by using the Orchestrator
D. Create two virtual machines that each host an instance of the application and set up a cluster
Answer: A
QUESTION 232
What is the result of a successful OAuth2 authorization grant flow?
A. The user has the application rights that correspond to the user’s role within the application’s database
B. The application is provided with a token that allows actions on services on the user’s behalf
C. The user has administrative rights to the application’s backend services
D. The third-party service is provided with a token that allows actions to be performed
Answer: B
QUESTION 233
A timeframe custom dashboard must be developed to present data collected from Cisco Meraki.
The dashboard must include a wireless health alert count.
What needs to be built as a prerequisite?
A. A publicly available HTTP server to receive Meraki Webhooks from the Meraki Dashboard API
B. A publicly available HTTP server to receive Meraki Webhooks from the Meraki Scanning API
C. A daemon to consume the Wireless Health endpoint of the Meraki Scanning API
D. A daemon to consume the Wireless Health endpoint of the Meraki Dashboard API
Answer: A
QUESTION 234
An application has these characteristics:
– provide one service or function
– distributed database
– API gateway
– central repository for code
– configuration database
– uses session management
Which two design approaches contribute to the scalability of the application? (Choose two )
A. built to scale based on a star topology
B. modular design iteration
C. session management in a stateless architecture
D. planned before the first device is deployed
E. distributed computing with tightly coupled components
Answer: AC
QUESTION 235
What is an effective logging strategy according 10 the 12-factor app tenets?
A. Capture togs by the execution environment and route to a centralized destination
B. Tag and save togs in a local document database that has querying capabilities.
C. Back up log files in a high-availability remote cluster on the public cloud
D. Timestamp and save logs in a local time-series database that has querying capabilities
Answer: A
QUESTION 236
Which two encryption principles should be applied to secure APIs? (Choose two.)
A. Use temporary files as part of the encryption and decryption process
B. Transmit authorization information by using digitally signed payloads
C. Use encrypted connections to protect data n transit
D. Reuse source code that contain existing UUIDs
E. Embed keys in code to simplify the decryption process
Answer: BC
QUESTION 239
A Cisco Catalyst 9000 switch has guest shell enabled.
Which Linux command installs a third-party application?
A. yum Install <package-name>
B. apt-get install <package-name>
C. zypper install <package-name>
D. dnf install <package-name>
Answer: A
QUESTION 240
Which function does Fluentd fulfill for application logging in Kubernetes?
A. logging agent for distribution
B. backend time series database storage
C. monitoring and log visualization
D. messaging queueig infrastructure
Answer: A
Resources From:
1.2021 Latest Braindump2go 350-901 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/350-901.html
2.2021 Latest Braindump2go 350-901 PDF and 350-901 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1mr2xSVIcLq2_l8ETudcq0FfZ3Ri8LMiL?usp=sharing
3.2021 Free Braindump2go 350-901 Exam Questions Download:
https://www.braindump2go.com/free-online-pdf/350-901-PDF-Dumps(184-217).pdf
https://www.braindump2go.com/free-online-pdf/350-901-VCE-Dumps(218-250).pdf
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!